Question: We're a small company. Why would anyone try to attack us?
Answer
We can all agree that large companies have more data than small companies. But all data is valuable to each company regardless of how much there is. Large organizations have the dedicated resources to continuously monitor, train, and defend against attacks and unintended human error. The majority of small and medium-size companies do not have these same cybersecurity skills on staff.
Hackers are aware of this security weakness. Even though their rewards are less, the time and effort required to do significant damage is often minimal. As a result, hackers are increasily targeting small and medium-size companies.
Question: Why would we be the target of a cyberattack or breach?
Answer
Think about all the day-to-day activities everyone in your company does. How many of these involve collecting, sharing, calculating, storing, and retrieving data?
emails
accounting
CRM
social media
Question: We have antivrus software so aren't we protected?
Answer
There was a time not very long ago when your legacy antivirus software was all your company needed. Viruses and malware were identified by your antivirus software provider, fixes were built, and all company devices were updated.
The speed of today's attacks requires a
proactive protection, not a dated reactive solution. Your company cannot afford to lock the door after an attacker has gotten inside. Malware often lives undetected on devices for months. It quietly listens, captures every keystroke, and steals your valuable data long before you know it's there. That's an alarming thought for any company leader.
How much damage could an undetected theft do not only to your company but also your customers?
access to your customer data
spoofing attacks using your email addresses
locking you out of your financial accounts
diverting money away from your accounts
What else can you think of?
We have backups. Can't we just recover from a backup?
Answer
Backups are essential for every company. No question about it. But consider these points:
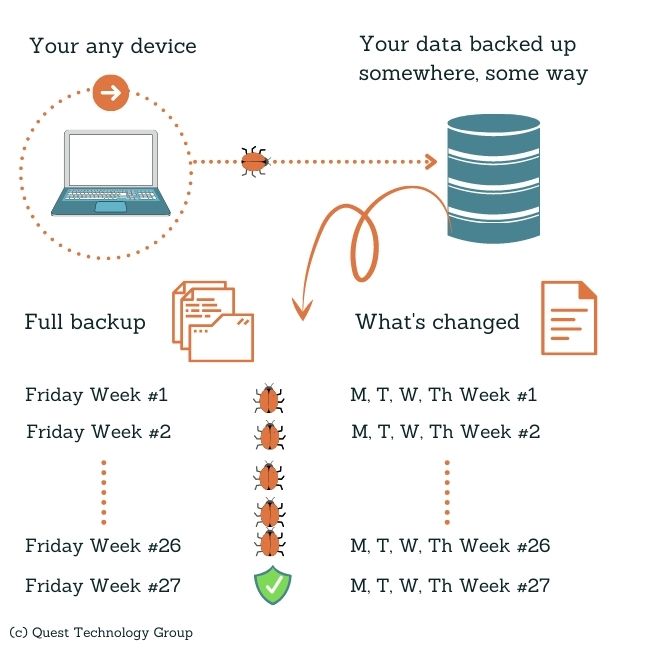
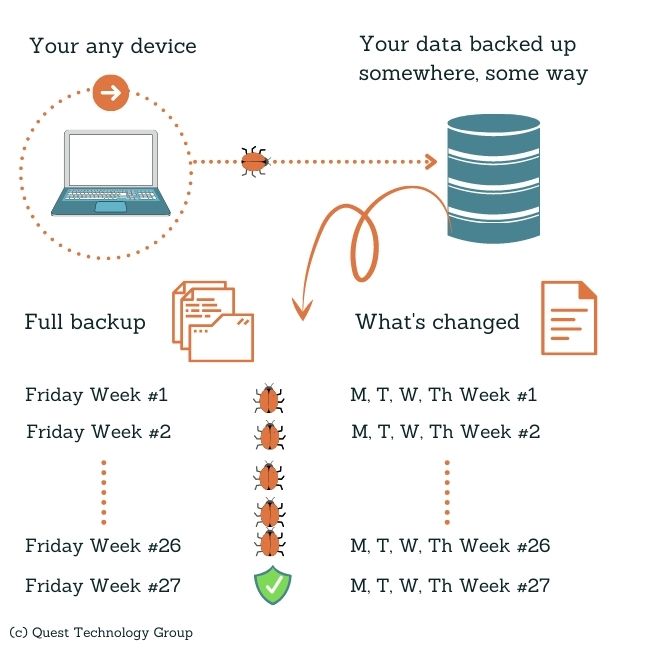
Because malware can live undetected inside your network and on devices for months, your backups might be compromised. How do you know you haven't been backing up this malware?
What proactive measures are in place to ensure that your backups are virus and malware free?
Once a breach is discovered, the trust your clients placed in you can quickly be lost. How do you rebuild that valued relationship?
What is the cost of rebuilding a relationship?
How likely is it that your attacker will return your stolen data? Restoring from backup does not recover the original lost data.
How long can you afford to be out of business while recovering from your backup?
How long will it take for you to feel confident that your company has been securely restored?
We're in the cloud. How would an attacker get our data?
Answer
Working in the cloud means your team has access to your company's software and data wherever they are. It's convenient and a way of business life we all have come to expect.
But expanding a company's network beyond the office walls also creates new risk opportunities.
We addressed above the need for a proactive next generation antivirus to replace your legacy antivirus. An important safeguard in next generation protection is the ability to manage all devices wherever they are. A centralized security protection policy eliminates a user's ability to interfere with a antivirus updates.
Think of being in the cloud as adding more doors to your secure office and leaving the key under every doormat.
Question: We have cyber insurance. Won't our insurance company reimburse our losses?
Answer
Insurance is not protection against an attempted attack or breach. While we expect insurance will help us recover our financial loss, it is not guaranteed.
Have you completely read the conditions in your
cyber insurance policy? For example, your policy will likely require that you have advanced endpoint security and MFA implemented. Do you have the documentation to support your implementation and results? If you have not met each of these terms, it is likely your claim will be denied.
In addition, insurance cannot restore the loss of trust, reputation, and customers. These all have long-term effects on your company that cannot be easily repaired.
Doesn't our MSP take care of cybersecurity for us?
Answer
When companies think of their managed service provider, they consider him their full-service IT provider. IT has a broad meaning to most people, but the actual scope of MSP services is very limited.
Traditional MSPs provide reactive remote and sometimes onsite support for servers, desktops, and laptops inside your physical location. They focus on applying Windows updates and responding to "it doesn't work" help requests.
Your remote, mobile, hybrid, cloud-based infrastructure requires a very different monitoring, skillset, and proactive approach. Cybersecurity professionals are trained, certified, and specialize not only in the basic MSP services but also the much broader areas of modern security.
It's critical that you ask your MSP what specific security services they are providing. They will likely tell you they support your in-house backups and a firewall. Backups and a firewall are not a comprehensive security solution. Most MSPs clearly exclude any responsibility for your data and the applications your business relies on.
This who does what on your
IT team matrix will help you plan the right skills for your company.
Cybersecurity sounds complicated. Where do we even begin?
Answer
Cybersecurity covers a lot of ground, and that can make it feel complicated. It's a concept that means something different to everyone.
Where do you even begin? You start with
small actionable steps that are right for your company.
When you have a clear roadmap that everyone in your company understands and can contribute to, cybersecurity becomes a lot less complicated.
Cybersecurity seems so expensive. How can we afford to implement all of the cybersecurity controls we need?
Answer
You need both trusted people and reliable tools that provide the best protection within your budget. That's why we recommend that you
start with the most important protection for your company.
It would be nearly impossible for any company, no matter their budget or resources, to implement everything at once. You and your team should start by aligning your security needs with your long term strategy. This will serve as your working roadmap. You will be able to successfully implement one practical thing at a time. Then you move on to the next step.