Protect What Your Business Depends On
Most leaders don't think about cybersecurity every day. They think about running their business.
What Leaders Actually Need to Know
The systems that your business depends on every day — your data, your workflows, your customer information — are all key parts of how your business runs. Protecting them isn't just a technical task; it's a leadership responsibility.
If you've said one or more of these things about protecting your company, you're like many business leaders.
But there's more to consider than just protecting your company. You have valued customers and clients who trust you to protect them too. Fortunately, implementing the right protection for your company doesn't have to be complicated or expensive.
It starts with committed leadership and step-by-step actions that focus on your business, not technology.
It starts with committed leadership and step-by-step actions that focus on your business, not technology.
You don't need to understand every threat, but it helps to start with clarity about a few practical questions:
What parts of our business would be most impacted if something went wrong?
How exposed are we really compared to what we expected?
Where are we relying on assumptions instead of having actual visible information?
Are we protecting what matters to our business, or just adding tools and services without a clear plan?
Who are we relying on to proactively monitor our risks and keep us informaed?
A Practical Approach
Protecting your business doesn't start with tools. It starts with understanding:
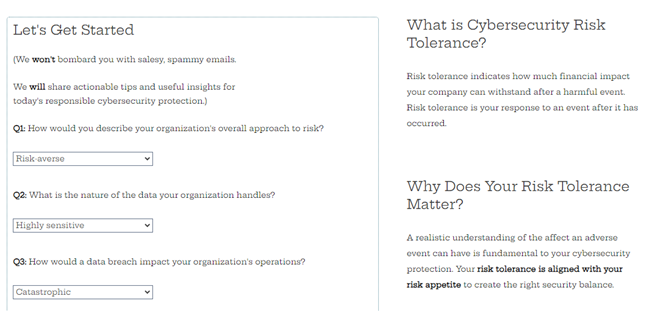
Clarify your cybersecurity risk tolerance
How much can you afford to lose when a security event happens?
High risk tolerance: You're able to withstand larger financial and reputational losses. Your focus is on maximizing profits at the expense of short-term losses.
Moderate risk tolerance: You seek a balance between risk impacts and potential profits from taking risks.
Low risk tolerance: Your priority is minimizing loss, negative events, and damage to your company.
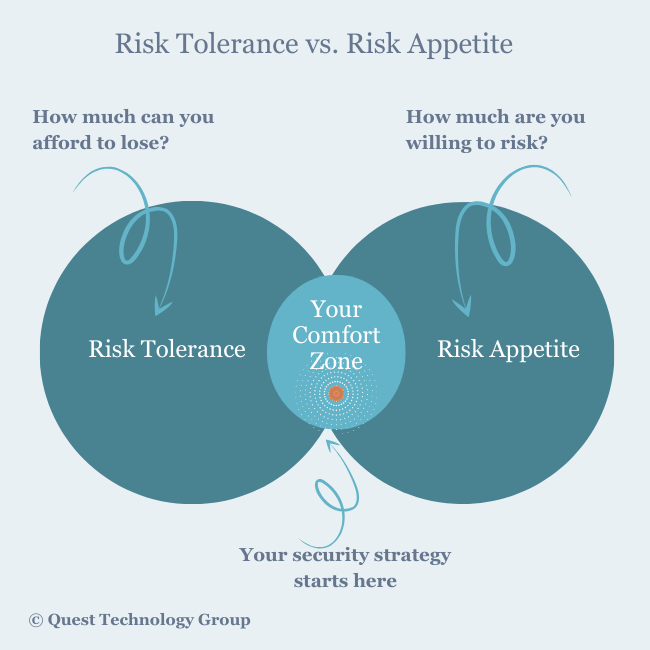
Clarify your cybersecurity risk appetite
How much risk are you willing to assume to achieve your long-term goals and strategies?
High risk appetite: This goes hand in hand with high risk tolerance. You are a risk-taker in anticipation of high rewards.
Moderate risk appetite: You're likely to take risks within your comfort zone.
Low risk appetite: You fall into the risk averse category. You are willing to sacrifice higher returns in both the short and long term for less risk exposure.
Discover your cybersecurity risk comfort zone
Every leader and company has its own cybersecurity comfort zone, the place where risk tolerance and risk appetite meet.
Start your cybersecurity planning there.
We're business owners and leaders like you are so we understand that sifting through the noise and information is sometimes just too much.
Here's a short ebook, Discovering Your Company's Unique Risk Posture, that you can read at your leisure. It includes a plain English explanation of the two risk types, how they impact your company's goals, and how to use these assessments to gain clarity and focus.
Grab Your Free Copy
Here's a short ebook, Discovering Your Company's Unique Risk Posture, that you can read at your leisure. It includes a plain English explanation of the two risk types, how they impact your company's goals, and how to use these assessments to gain clarity and focus.
Grab Your Free Copy
What About Cyber Insurance?
Myth: We've heard business leaders say they have cyber insurance coverage so they're not concerned about security risks. Their insurance company has them covered. Not so.
What is Cyber Insurance?
Cyber liability is specialized business insurance coverage. This coverage is in addition to your company's general liability insurance policy and is often specifically excluded under this policy. Every insurance company has its own set of coverages, limitations, and exclusions so a careful review with your insurance agent, broker, or company representative is essential.
What is Covered by Cyber Insurance?
According to the FTC's cybersecurity resources for small business, these are coverages you should have included in your cyber insurance policy:
What Are Insurance Companies Requirements for Cyber Liability Coverage?
Regardless of your current insurance carrier or policy, it is important to keep these points in mind: