Understand the baffling technology words and phrases you hear every day.
The Internet
What is a Browser
What is Cache
What is a Cookie
What is Data in Transit
What is Data at Rest
What is a Data Packet
What is DNS
What is Encryption
What is End-to-End Encryption
What is HTTP/HTTPS
What is SSL/TLS
Your Company Network
What is Antivirus Software
What is DNS Content Filtering
What is Advanced Endpoint Security
What is a Firewall
What is a Modem
What is a Network
What is Remote Desktop (RDP)
Work from Anywhere
What is a Home Network
What is a Hotspot
What is a VPN
What is Wi-Fi
Life in the Cloud
What is the Cloud
Your Company Assets
What is Access Rights
What is a Data Inventory
What is Shadow IT
What is a Software Inventory
What is a Technology Roadmap
What is IT Asset Management (ITAM)
What are User Access Rights
Your Security Essentials
What is a Brute Force Attack
What is Credential Stuffing
What is an IP Blacklist
What is a Keylogger
What is Malware
What is Warshipping
What is a Whitelist
What is a Browser
What is Cache
What is a Cookie
What is Data in Transit
What is Data at Rest
What is a Data Packet
What is DNS
What is Encryption
What is End-to-End Encryption
What is HTTP/HTTPS
What is SSL/TLS
Your Company Network
What is Antivirus Software
What is DNS Content Filtering
What is Advanced Endpoint Security
What is a Firewall
What is a Modem
What is a Network
What is Remote Desktop (RDP)
Work from Anywhere
What is a Home Network
What is a Hotspot
What is a VPN
What is Wi-Fi
Life in the Cloud
What is the Cloud
Your Company Assets
What is Access Rights
What is a Data Inventory
What is Shadow IT
What is a Software Inventory
What is a Technology Roadmap
What is IT Asset Management (ITAM)
What are User Access Rights
Your Security Essentials
What is a Brute Force Attack
What is Credential Stuffing
What is an IP Blacklist
What is a Keylogger
What is Malware
What is Warshipping
What is a Whitelist
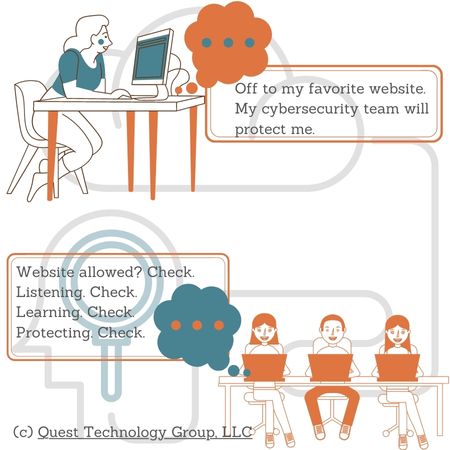
What is Advanced Endpoint Security?
Unlike legacy antivirus software that is mostly reactive, today's sophisticated security tools are proactive. This software continually listens, monitors, scans, and prevents threats before they happen.
How Does Advanced Endpoint Security Work?
Devices on the company's network are referred to as endpoints. These include desktops, laptops, servers, and mobile devices. Software is installed on each endpoint as well as on centrally-managed servers.
This software uses machine learning and AI to teach itself what potential threats might be. This means that advanced security software can detect and block attacks even as they are happening.
Malware and viruses don't reach the device. With legacy antivirus, viruses are detected and removed after they infect the device. Which would you prefer?
Advanced security software includes tools that block users from accessing potentially dangerous sites as well as from downloading or installing unauthorized apps and software.
Some key advantages to advanced endpoint security over legacy antivirus include ---
Keep Discovering
What's the Difference Between Antivirus and Advanced Endpoint Security?
How Website Blocking Protects Your Company
Why a Company Shadow IT Policy is Important